No products in the cart.
2.27 million computers hacked using CCleaner, including yours? Leave a comment
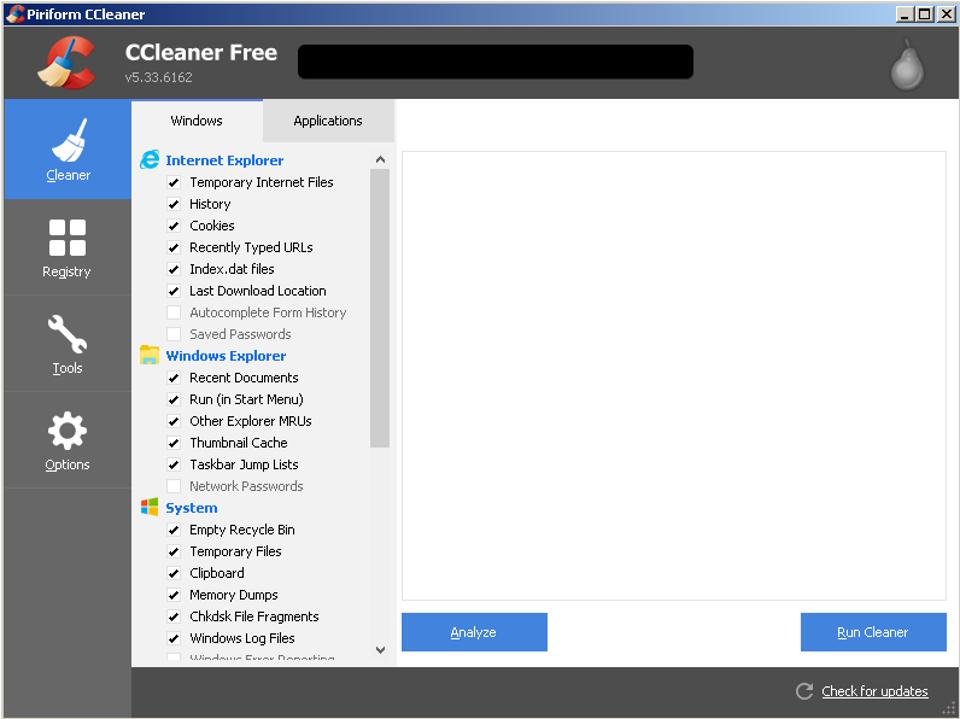
CCleaner was recently hacked, If you are running CCleaner v5.33.6162 or CCleaner Cloud v1.07.3191 for 32-bit Windows computers. Please remove it immediately and update to version v5.34 to avoid Computer hack.
CCleaner was hacked recently which affected mostly 32 bit windows operating systems and CCleaner released an update to patch the exploit but its won’t update itself to the latest version. unfortunately, all the users have to update it manually.
CNET wrote an article about this hack and the crux of the matter is, it only gathers your computer information like IP address, computer name, a list of installed software on your computer, a list of active software and a list of network adapters and sends it to a third-party computer server.
The good news is that your passwords and credit card information is safe. It only infected around 3 percent of the total users which comes to 2.27 million computers.
ITLINKS informed all its clients and posted on their social media regarding this hack.
ITLINKS recommends its users to use an antivirus as my own antivirus informed me about the exploit and that my CCleaner needed to be immediately updated.
Secondly, ITLINKS recommends to keep your computer updates on and your computer up to date to shield against such hacks.
Frobes calls this an assault on AVAST. Here is the article from frobes
When Avast learned that its CCleaner security software had been infectedwith a backdoor by unknown hackers, they thought any real damage had been avoided, even though 2.27 million had downloaded the tainted tool. But that initial analysis was wrong, according to new information straight from Avast, which said Thursday it was likely the hackers had dropped more sophisticated malware inside technology and telecoms companies, with victims likely in the hundreds.
That analysis came after Cisco’s Talos security division released research late Wednesday naming a handful of technology companies that were targeted with “secondary payloads” over just four days in September, saying 20 victim machines were infected as a result. Cisco, Microsoft, VMware, Intel, Sony, Samsung, HTC, Linksys, D-Link and Singtel Corp were all on a list of targets, according to Talos, though it’s unclear which were amongst the overall eight that Avast said had PCs infected. “This would suggest a very focused actor after valuable intellectual property,” Cisco’s researchers added.
Avast concurred with Cisco’s research, but said it was likely more were infected. “Given that the logs were only collected for little over three days, the actual number of computers that received the 2nd stage payload was likely at least in the order of hundreds,” wrote CEO Vince Steckler and chief technology officer Ondrej Vlcek. Researchers were only able to look across those days as the hacker server they had access to had its logs wiped on September 12 when it ran out of memory, Vlcek told Forbes.
A smart attack
What was clear to both Avast and Cisco was that this was a sophisticated targeted attack on the tech industry. Showing just how the attackers were carefully selecting their targets, more than 700,000 computers of the 2.3 million infected reported back to the hackers’ server over few days the researchers were able to gather data, Cisco found. But just over 20 machines were hit with the second-stage attack, in which “reconnaissance information” about infected computers, such as IP address and software active on the machine, were sent to the attackers.
“When combined, this information would be everything an attacker would need to launch a later stage payload that the attacker could verify to be undetectable and stable on a given system.,” Cisco added.
“At the time the server was taken down, the attack was targeting select large technology and telecommunication companies in Japan, Taiwan, UK, Germany and the US,” Avast added. The company has contacted firms targeted, but isn’t disclosing names.
Vlcek told Forbes that the eight affected companies had been contacted, indicating some victims had more than one PC infected. He said the second payload was “a stage of a multi—stage attack.” “It doesn’t do anything malicious… all it’s doing is basically waiting for a command to update it for a third-stage,” he added. The investigation now moves on to determine whether or not that third-stage was activated.
Cisco is recommending any organization affected to not just remove the affected version of CCleaner 5.33 or update, but should restore from backups or reimage systems entirely to get rid of malware.
As for who was behind the attack, Cisco said it was worth looking into claimsfrom Russian security firm Kaspersky that a known, sophisticated group of hackers variously known as Axiom and Group 72, previously linked to Chinese hackers. There appeared to be code overlap between the CCleaner backdoor and Group 72’s malware. Vlcek said he didn’t know if a nation state was behind the attack and it’d be unlikely for anyone to find out. “This looks … like an espionage-type attack,” he added.
Avast continues to cooperate with police to chase them down. “We have continued working with law enforcement units to trace back the source of the attack. We are committed to getting to the bottom of who is behind this attack,” the CEO and CTO added.